After telling the installation of Cuckoo and dynamic analysis of the suspected software there are easier ways to do the analysis of the malware. The aim of our analysis is to understand if a file that we downloaded or sent by email is harmful or not. We will have two steps:
- Use Virustotal to check the file with 54 antivirus databases
- Dynamic analysis of the file with ThreatExpert
Use Virustotal to check the file with 54 antivirus databases:
The first step will be to check with http://www.virustotal.com . I will use an older virus named Sality to see what will be the results. At the moment Virustotal uses 54 different antivirus database to check the file. Here is the result from Virustotal. As you can see it was recognized by 45 different antivirus software.
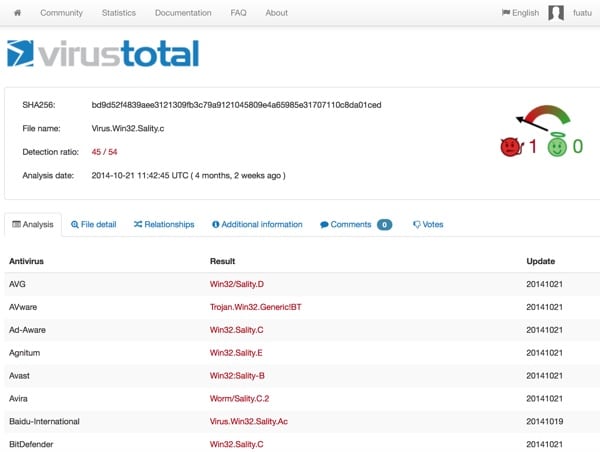
After this step you can be sure that this is a malware. However assume a case that you have a new virus which is not known by any antivirus. In this case to be sure we still need to make a dynamic analysis to see if there is any harmful behavior.
Dynamic analysis of the file:
For dynamic analysis we will use http://www.threatexpert.com/submit.aspx.
Update: 08 December 2019 Threadexpert site is no more https://app.any.run/ is a very good alternative to use.
The definition from its website: “ThreatExpert is an advanced automated threat analysis system designed to analyze and report the behavior of computer viruses, worms, trojans, adware, spyware, and other security-related risks in a fully automated mode.”
When you submit the file it will ask for and email address. When the analysis is complete it will send the analysis details by email and also will provide a URL for the report.
Here is the report link for Sality: http://www.threatexpert.com/report.aspx?md5=52ae3b7f8f383f169363b5d4f5d5deca
And here is the screenshot below: In the screenshot you can see that it already shows harmful behavior. It also gives some antivirus software results.

As a result I suggest to use Virustotal and ThreatExpert for the analysis of unknown and suspicious files if you really must execute them.
More links here
– The end of post –