Create your own VPN server for free easily. No coding or extensive knowledge required. Outline is a great free VPN tool to manage everything. Go to https://getoutline.org/get-started/ web site download the Outline Manager for your Mac, Linux or Windows machine. Follow up the steps and you will have you own […]
Security
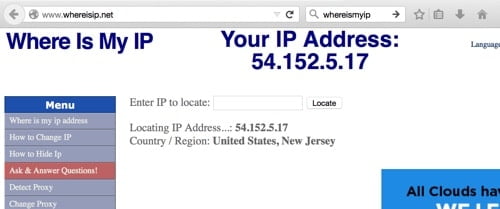
You need your own server where you can connect with SSH as a prerequisite for ssh tunneling. For this purpose you can use “Amazon Web Services Free Tier EC2 instances” or “Google Cloud Platform Free Tier – Compute Instances“ We will use a port for the tunneling and use our […]
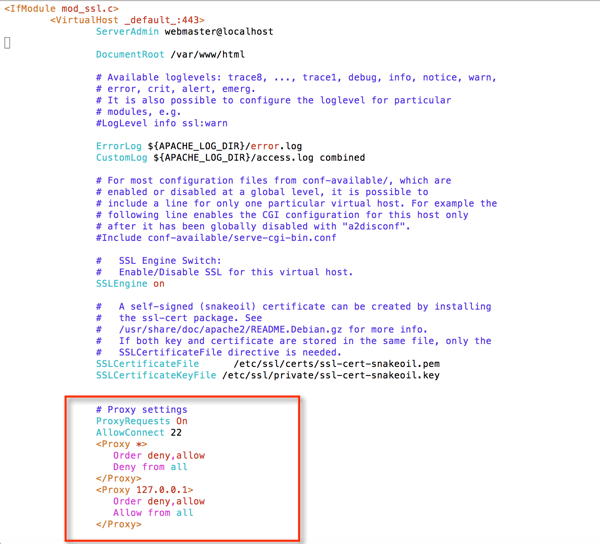
SSH tunneling over https to bypass firewalls Check first “SSH Tunneling” if you need more details before starting with “SSH tunneling over https”. In this topic we will learn how to bypass firewall that blocks SSH at application level using “SSH tunneling over https”. This will also bypass web proxy […]
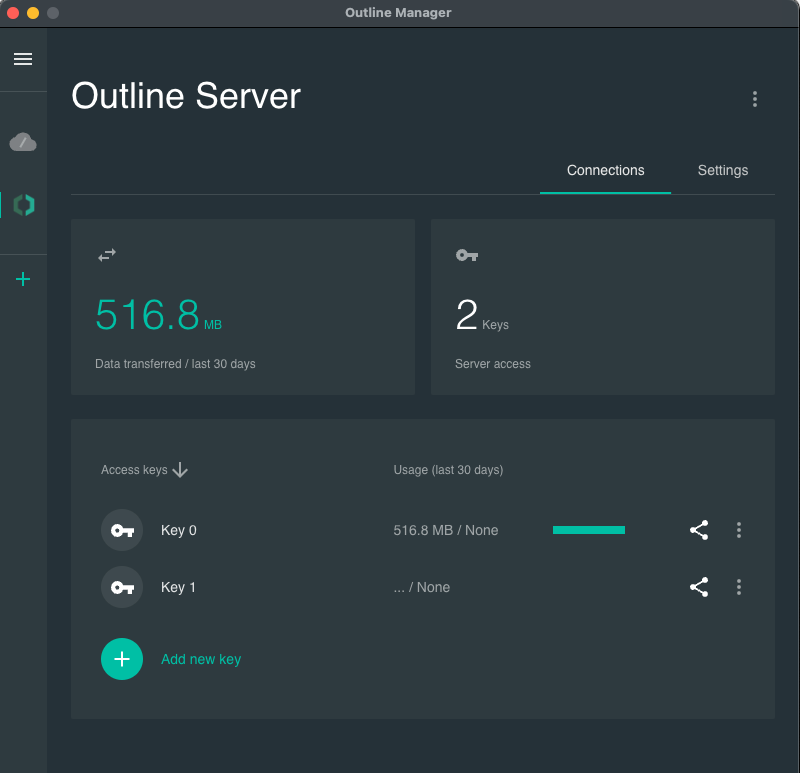
You can install your own free VPN server for free and can use it for Windows, MacOS, Linux, Apple devices and Android devices without paying a single penny. And what is more there will be no logs for your connections if you do not want to. You can also delete […]
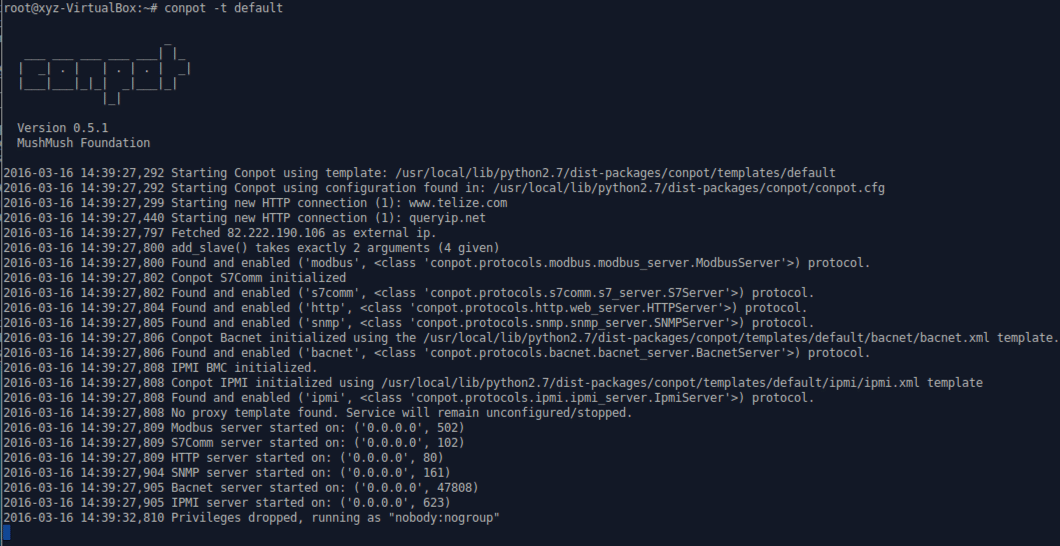
In this subject we will follow a step by step instruction of installing an Industrial Control System honeypot. We will use CONPOT. The URL for it is http://conpot.org and for documentation check: https://github.com/mushorg/conpot/tree/master/docs. The default configuration of Conpot simulates a basic “Siemens SIMATIC S7-200 PLC” with an input/output module and a CP […]
After telling the installation of Cuckoo and dynamic analysis of the suspected software there are easier ways to do the analysis of the malware. The aim of our analysis is to understand if a file that we downloaded or sent by email is harmful or not. We will have two […]